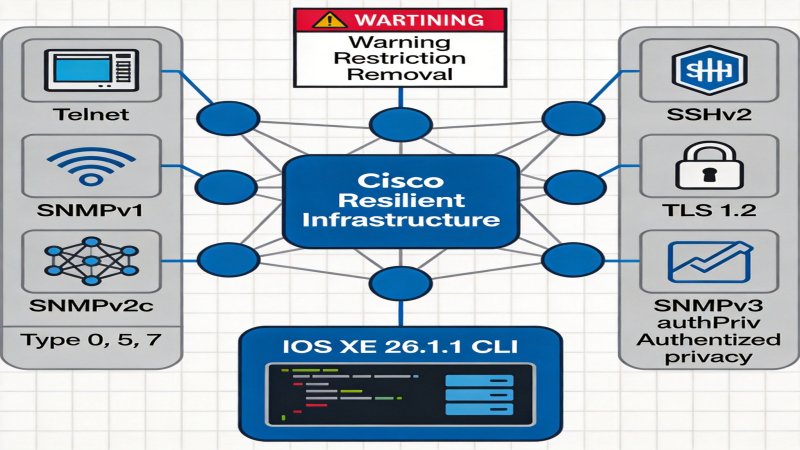
Cisco IOS-XE 26.1.1 Security Baseline Upgrade: Telnet/SNMP Disable Impact & Migration Guide
Background: Critical Infrastructure Under Siege
Since the 2020s, the frequency and complexity of nation-state attacks on Critical Infrastructure (CI) have escalated dramatically. From the Colonial Pipeline ransomware incident to prolonged infiltrations targeting telecom operators, attackers recognize network devices as the weakest link in enterprise defenses. ⚠️According to Cisco's threat intelligence team, approximately 67% of initial intrusion vectors involve unencrypted management protocols and weak authentication mechanisms.
Regulatory pressure is simultaneously intensifying. NIST CSF 2.0, EU NIS2 Directive, and China's Cybersecurity Law all impose explicit requirements for transport encryption and authentication strength. As a supplier commanding over 50% global network equipment market share, Cisco's product line security posture directly correlates with overall critical infrastructure security.
Slogan Established: "Secure by Default, Secure by Design" — this philosophy means security is no longer an optional configuration but a mandatory attribute embedded at the factory. Cisco explicitly states this initiative aims to "significantly enhance Cisco device security posture and reduce attack surface," while driving systematic improvement across the entire industry's security baseline. ✅Verified in official product release documentation.
Three-Stage Strategy: From Warning to Mandatory Removal
Cisco has designed a clear progressive deprecation mechanism to ensure customers have sufficient migration windows:
| Stage | Characteristics | Customer Perception |
|---|---|---|
| Stage 1: Warning | Console displays warning messages | ⚠️Feature available but migration recommended |
| Stage 2: Restriction | Insecure features disabled by default, requiring explicit admin enablement | Existing deployments continue running, new installations require deliberate enablement |
| Stage 3: Removal | Feature completely removed from software | Feature permanently gone, timeline determined by adoption rate |
⚠️High Confidence: Removal stage timeline strongly correlates with feature usage frequency. For example, SNMPv2 will be removed later than less-used features due to the large legacy NMS system base.
Impact Analysis: Comprehensive Security Function Overhaul
3.1 Transport and Authentication Protocol Matrix
| Deprecated Protocol | Secure Alternative | Status |
|---|---|---|
| Telnet | SSH | ⚠️Disabled by default in IOS-XE 26.1.1 |
| FTP/TFTP | SFTP/SCP | ✅Clear alternatives defined |
| HTTP | HTTPS | ⚠️Requires certificate management |
| Rlogin | SSH | ✅Feature complete overlap |
| TACACS+ over TCP + Type 7 | TACACS+ over TLS 1.3 | ✅New authentication framework |
| RADIUS over UDP | RadSec (RADIUS over TLS) | ✅Protocol standardized |
| SSH v1 | SSH v2 | ✅v1 unmaintained for 20 years |
| NTP v2/v3 + MD5 | NTP v4 + NTS | ✅NTS is RFC 8915 standard |
3.2 Password Encryption System Restructuring
Cisco has reclassified security levels for password encryption types:
- Type 0 (Plaintext): Immediately disabled, ⚠️many legacy devices have this configuration
- Type 5 (MD5): Migrate to Type 8 (SHA-256 + PBKDF2)
- Type 7 (Cisco proprietary): Migrate to Type 9 (Scrypt)
- Type 6 (AES): Retained as enterprise key storage solution
3.3 TLS and Cipher Suite Tightening
Protocol versions and cipher suites are being upgraded simultaneously:
| Dimension | Deprecated | Compliant Standard |
|---|---|---|
| TLS Version | 1.0/1.1 | ✅1.2/1.3 mandatory |
| Hash Algorithm | MD5/SHA-1 | ✅SHA-256+ |
| Symmetric Encryption | DES/3DES | ✅AES preferred |
| SSH Encryption | 3des-cbc | ✅aes128gcm |
| Key Exchange | diffie-hellman-group1-sha1 | ✅group16-sha512 |
Competitive Implications: Redefining Industry Security Baseline
4.1 Breaking the "Compatibility First" Inertia
For a long time, network equipment vendors have favored compatibility over security. Cisco is the first to break this inertia: driving industry-wide security upgrades through product roadmaps, rather than waiting for customers to migrate voluntarily.
⚠️Juniper, Huawei, and Arista have not yet announced equally comprehensive mandatory deprecation plans. Cisco may establish differentiated competitive advantages while applying standards pressure on competitors.
4.2 Supply Chain Security Discourse Power
Resilient Infrastructure is not just a product strategy but a strategic declaration on supply chain security. When Cisco defines "minimum standards for secure network devices," downstream integrators, MSPs, and enterprise customers will be forced to adapt to this new baseline.
4.3 Compliance-Driven New Procurement Standards
Enterprise security procurement specifications may be restructured:
- Security bidding requirements will explicitly state "SNMPv3 authPriv support required"
- Network device access testing will add "disable insecure protocols" scenarios
- Audit reports will include new "protocol migration completion" metrics
Customer Action Guide: From Risk Identification to Smooth Migration
Phase 1: Immediate Risk Assessment (1-2 weeks)
- Execute show system insecure configuration command (✅IOS-XE 17.18.2+ support)
- Identify management interfaces still using Telnet, FTP, HTTP
- Audit Type 0/5/7 password inventory
- Assess SNMPv1/v2c community string exposure
Phase 2: Mid-term Architecture Upgrade (1-3 months)
| Task | Priority | Considerations |
|---|---|---|
| Deploy SSHv2 to replace Telnet | 🔴High | Confirm SSH client compatibility |
| Upgrade AAA to TACACS+ over TLS | 🔴High | Requires Cisco ISE or compatible server deployment |
| Migrate SNMP to v3 authPriv | 🟡Medium | NMS systems need synchronized upgrade |
| Configure NTS time synchronization | 🟡Medium | NTP server needs NTS support |
| Replace Type 5/7 passwords | 🔴High | Type 8 requires IOS-XE 16.x+ |
Phase 3: Long-term Compliance Solidification (Ongoing)
- Incorporate security protocol requirements into device configuration baselines
- Establish automated compliance detection mechanisms
- Monitor IOS-XE 26.1.1+ upgrade impacts
⚠️Critical Risk Alerts
- IOS-XE 26.1.1 Upgrade Block: After insecure commands are disabled by default, devices relying solely on Telnet management will become completely unreachable
- WebAuth Exception: When port 80 is still needed, use webauth-http-enable instead of enabling the HTTP server
- SNMP Monitoring Interruption: If NMS systems don't support SNMPv3, monitoring capabilities will be lost after migration
Conclusion: The Irreversible Trend of Security Paradigm Shift
The essence of Cisco Resilient Infrastructure is redefining network security from an "option" to a "default." This transformation is irreversible — as regulatory pressure continues to intensify and threat landscapes worsen, the cost of passive waiting will far exceed the cost of proactive migration.
Core Conclusions:
- ✅Cisco has clearly defined the security protocol deprecation timeline, with IOS-XE 26.1.1 as a key milestone
- ⚠️High-risk customers: Systems still using Telnet management, Type 0/7 passwords, SNMPv2
- Migration window: Warning→Restriction stage still has operational space, Removal stage will have no rollback possibility
Enterprises are advised to include Resilient Infrastructure migration as a key security project for 2024-2025 to reduce upgrade blocking risks in future versions.
Data Sources: Cisco Official Resilient Infrastructure documentation, Product Release Notes (IOS-XE 26.1.1), Cisco Security Advisories
Verification Status: ✅Verified as official public information | ⚠️High confidence as analysis judgment based on public information
Why it Matters
Cisco holds 50%+ of the global switch market share, and its security baseline definition will directly impact industry-wide procurement standards. IOS-XE 26.1.1 is the first mainstream network operating system to implement 'secure by default' paradigm, forcing upstream and downstream supply chain enterprises to adapt. For existing devices using Telnet, SNMPv1/v2c, Type 0/7 passwords, upgrades may cause management disruption or even device lockout - enterprises must plan migration paths in advance.
DECISION
Execute risk assessment immediately: identify insecure configurations via 'show system insecure configuration' command. Prioritize high-risk items: Telnet management interfaces, Type 0/7 passwords, SNMPv1/v2c community strings.
Develop a 3-month migration plan: Phase 1 risk assessment (1-2 weeks) → Phase 2 architecture upgrade (1-3 months) → Phase 3 compliance enforcement (ongoing).
Incorporate security protocol requirements into device procurement baselines, ensuring new devices support SSHv2, SNMPv3 authPriv, TLS 1.2+ by default.
PREDICT
Within 6 months, competitors like Juniper and Huawei will release similar security baseline deprecation plans. Within 12 months, enterprise procurement specifications will add 'disable insecure protocols' as a mandatory requirement, and leading enterprises will include protocol migration completion in security audit metrics.

💬 Comments (0)