In-Depth Technical Analysis Report: Claude Mythos and Project Glasswing
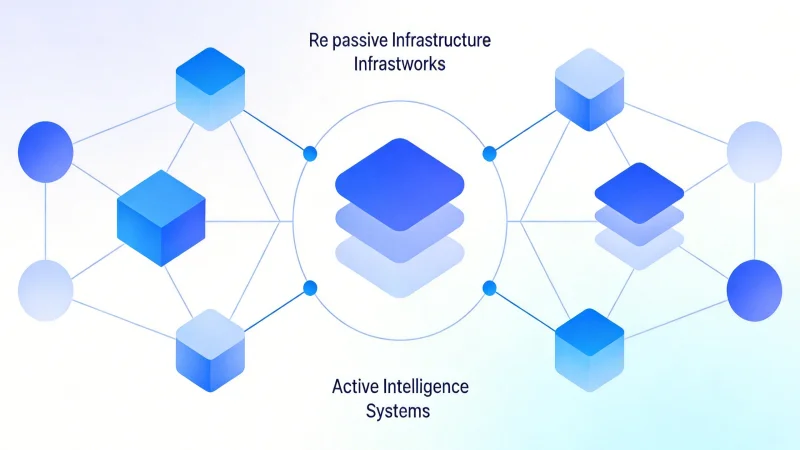
This report analyzes the four-layer AI security governance stack built by Claude Mythos and Project Glasswing. It features autonomous security agents using multimodal Transformers and reinforcement learning, hardware-accelerated privacy computing, and a standardized alliance framework for end-to-end automated defense. Key strengths are its adaptive, evolutionary defense concept and open ecosystem. Major open challenges include the RL simulation-reality gap, trust/privacy in alliance collaboration, automation accountability, and adversarial risks against the defensive AI itself.