I. From Capability Listing to Scenario Protection
AI Agent deployment spans multiple independent battlegrounds across external networks, internal networks, cloud, and endpoints. This report analyzes protection capabilities and gaps across seven deployment scenarios for Cisco, PANW, and Fortinet.
The threat model draws on OWASP ASI and the Promptware Kill Chain (7 stages). Key finding: prompt injection is only Stage 1 (93.3% success rate vs auto-approve), attackers traverse 4+ stages — each stage presents an interception opportunity, provided the protection covers it.
II. Seven-Scenario Protection Comparison
Scenario 1: Cloud LLM API Calls (External)
Cisco leads: AI Defense Runtime detects 200+ attack techniques (45+ injection), inline SSE interception, predictive DNS defense. PANW AIRS + Portkey comprehensive but SaaS-only. Fortinet FortiAIGate (NVIDIA Nemotron + GPU) architecturally sound but FortiSASE AI capabilities lag.
Scenario 2: Internal Coding Agents (Internal + External)
All three have major gaps. The core problem is Confused Deputy — agents hold high-privilege credentials but cannot distinguish legitimate requests from injected instructions. Clinejection (GitHub issue title prompt injection → 4,000 malicious downloads) and GTG-1002 (nation-state actor decomposes attacks into seemingly reasonable substeps) prove attacks are operational. PANW Koi is the only dedicated solution ($400M acquisition, productization pending). No vendor detects malicious code generation.
Scenario 3: MCP Toolchain (Internal + External)
PANW leads via Portkey Gateway (trillion-token/month) + AIRS MCP Threat Detection + Supply Chain Defense. Critical distinction: Fortinet DPI signatures (5 appids) detect whether MCP traffic exists, not whether it is safe — necessary but insufficient. Cisco MCP Gateway only works at external SSE layer. Tool description injection is a shared blind spot.
Scenario 4: Agent Data Access and DLP (Internal + External)
Fortinet leads internally: FortiOS native DPI DLP + Enhanced DLP with OCR. PANW Idira (ZSP + JIT) is the only agent-level just-in-time access control. Cisco SASE DLP covers external egress only. RAG poisoning is underestimated — Cisco is the only vendor with RAG security detection.
Scenario 5: Shadow AI Detection (External)
Cisco advantages: AI classification constitutional model (LLM-automated AI app taxonomy) + predictive DNS. Fortinet AIAP database + Shadow AI visibility for compliance. PANW has no standout differentiation.
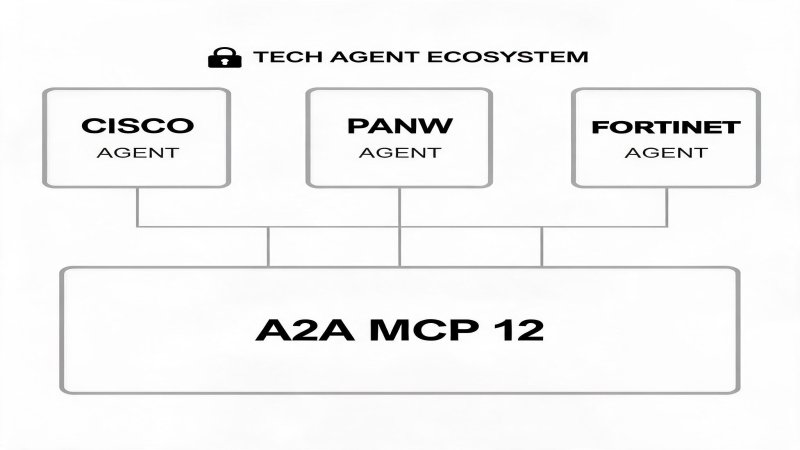
Scenario 6: A2A Multi-Agent Collaboration (Internal)
Shared blind spot across all three. A2A protocol specification lacks security standards (no message signing, authentication, or semantic integrity). Fortinet DPI signatures can see A2A traffic but cannot evaluate content. Cascading failure containment requires hardware-level deterministic isolation (Fortinet ASIC, Cisco DPU firewall). This is the next startup blue ocean.
Scenario 7: Operations Agents (Internal)
Operations agents hold the highest privilege and destructive potential. All three focus on discovery + auditing rather than prevention + containment. Automatic rollback is critical but none offers it. PANW AgentiX three-mode operation (autonomous/semi-auto/human-confirm) is the only risk-tiered execution solution.
III. Scenario Coverage Matrix
| Scenario | Network | Cisco | PANW | Fortinet |
|---|---|---|---|---|
| 1 Cloud LLM | External | 5/5 | 4/5 | 3/5 |
| 2 Coding Agent | Int+Ext | 3/5 | 3/5 | 2/5 |
| 3 MCP Toolchain | Int+Ext | 4/5(ext)/2/5(int) | 5/5(cloud)/2/5(int) | 2/5(detect only) |
| 4 Data DLP | Int+Ext | 3/5(ext)/2/5(int) | 4/5(ext)/2/5(int) | 5/5(int)/3/5(ext) |
| 5 Shadow AI | External | 5/5 | 3/5 | 4/5 |
| 6 A2A Collab | Internal | 2/5 | 2/5 | 2/5 |
| 7 Ops Agent | Internal | 3/5 | 3/5 | 4/5 |
IV. Five Key Judgments
1) MCP toolchain is the 12-month battleground: Server explosion + tool poisoning + confused deputy attacks operationalized. PANW leads via Portkey, Cisco external-only, Fortinet protocol-layer only.
2) Coding agents are the highest-risk blind spot: Clinejection and GTG-1002 prove attacks are real. Koi is the only dedicated solution but not yet productized.
3) JIT access is the DLP differentiator: Agent data access must be just-in-time. PANW Idira is the only option, Cisco Astrix in progress, Fortinet has nothing.
4) A2A security is the next blue ocean: Protocol-level security standards are fundamentally missing. Whoever ships A2A identity + message integrity + cascade containment first owns a new category.
5) Galileo observability is Cisco's undervalued dark horse: As agents go production, hallucination/bias/cost detection becomes essential. Only Cisco can do this.

💬 Comments (0)