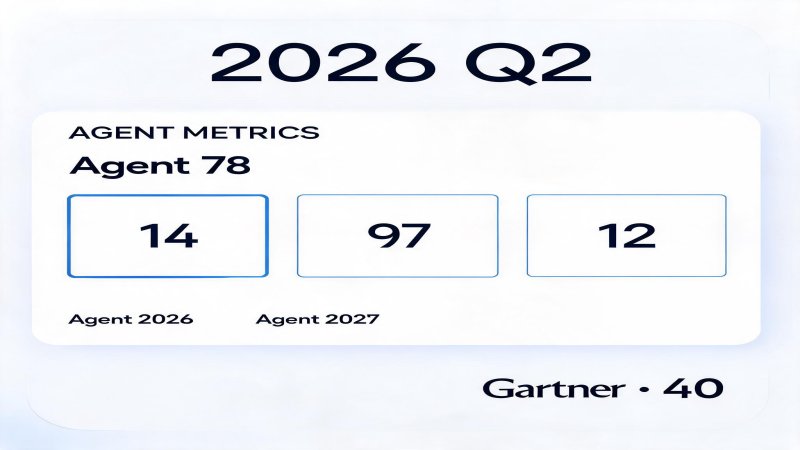
Data Landscape: The Harsh Reality of 78% Pilots, 14% Scale
2026 Q2 reveals a clear yet brutal gap in enterprise Agent deployment: pilots are widespread, but mass production remains scarce.
A survey of 650 enterprises shows 78% are advancing Agent pilot projects, but only 14% have achieved scaled deployment ✅. Another survey of AI operations teams (AiiNova) confirms this divide: 79% remain in exploration, with only 11% in production and just 2% achieving scale ✅.
Gartner's CIO survey offers more conservative figures: 17% deployed ✅. Fivetran adds a critical insight: among enterprises with deployed Agents, 41% in production use, but only 15% feel fully prepared ✅.
Security alarms are louder. Arkose Labs shows 97% of security leaders expect Agent security incidents within 12 months ⚠️Vendor Claim; 88% of enterprises have already reported at least one Agent-related security incident ⚠️High Confidence. UiPath reveals the core anxiety: 56% of enterprise IT security teams cite Agent security as the top concern ✅.
But mass production pays off. Successful scaled Agent projects show median ROI of 171% ✅; ServiceNow's case is most representative—AI Agents achieving 80% autonomous handling rate, delivering $325M annualized value ✅.
Industry divide is notable. Financial industry: 21% at scale vs. Healthcare: 8% ✅. 89% of scaled enterprises have deployed observability systems ✅, confirming strong correlation between security infrastructure and scale.
Gartner's warning: 40%+ of Agent projects expected to be cancelled by end of 2027 ✅.
The Gap Essence: Model Capability Is Not the Bottleneck, Governance Infrastructure Is
Why hasn't 78% pilot success translated to 14% scale? The core issue isn't model capability.
Among five major scale-failure reasons, governance infrastructure deficit ranks first, far ahead of model performance, compute costs, or talent shortage. Enterprises discovered that Agent "autonomy" is an advantage in pilots but a risk at scale—Agents are no longer just Q&A tools but digital workers capable of cross-system actions, API calls, and task execution.
Three fundamental challenges:
Identity Vacuum: Traditional IAM systems are built on "human user + session" models. Agents break this paradigm—operating without sessions, triggering workflows autonomously, using service accounts instead of personal credentials. Enterprises lack visibility into Agent identities, let alone behavior chains.
Permission失控: When Agents hold long-lived API keys or OAuth Tokens for sensitive systems, the static "verify-authorize-access" model fails completely. A goal-justified but path-anomalous Agent behavior may bypass all identity checks yet cause catastrophic outcomes.
Black Box Operation: Agent decision opacity prevents traditional logs and audit frameworks from distinguishing "human-initiated" from "Agent-autonomous" operations. Process-tree-level behavior tracking remains absent in most enterprises.
Cisco's RSAC 2026 data confirms: 85% running Agent pilots, only 5% in production ✅—an 80 percentage point gap is governance capability gap.
Vendor Q2 Positioning: Five-Layer Architecture, Five Tracks
From February to May 2026, five core vendors—Microsoft, Cisco, Palo Alto, NVIDIA, OpenAI—intensified positioning in Agent security.
| Layer | Microsoft | Cisco | Palo Alto | NVIDIA | OpenAI |
|---|---|---|---|---|---|
| Entry Identity & Access | Entra Agent ID Blueprint Templates | Duo IAM Astrix Acquisition NHI Discovery | Portkey Acquisition AI Gateway | — | Daybreak Three-Tier Access (GPT-5.5-Cyber) |
| Assessment Red Team & Vuln Discovery | MDASH 100+ Agent Orchestration 16 CVE Discovery | AI Defense Explorer Edition LLM Security Leaderboard | Unit 42 Frontier AI Defense Exposure Analysis | — | Codex Security Threat Modeling 3000+ Vuln Fixes |
| Guardrails Runtime Security | Agent 365 Built-in Policies MCP Protocol Support | DefenseClaw Open Source MCP Gateway | Prisma AIRS 3.0 Agent Guardrails | OpenShell Open Source Sandbox Isolation 17 Platform Integration | — |
| Detection Behavior Monitoring | Copilot Studio Governance Agent 365 Control Plane | AI Defense Runtime Secure Access SSE Behavior Analysis | Cortex Cloud 2.0 AgentiX Workgroups Day to Minute Remediation | NemoClaw Audit Trail | Daybreak Continuous Monitoring Audit Reports |
| Response Incident Handling | Defender Integration SOC Orchestration | Splunk AI Automated Response Machine-Speed Response | — | — | Daybreak Patch Validation Automated Remediation |
Track 1: Entry Layer Identity & Access Control
Entry layer is the starting point for Agent security, addressing "who can do what" boundaries. Microsoft and Cisco lead here.
Microsoft's Entra Agent ID is the first enterprise-grade Agent identity framework. Each Agent receives an independent identity object (Object ID), enabling batch creation via Blueprint templates with Conditional Access directly applied to Agent identities. The Sponsor mechanism binds each Agent to a specific owner, solving the "no accountability" governance vacuum. Integrated into Agent 365, Walmart deployed 1200+ Agents ✅.
Cisco builds a dual-track identity system through Duo IAM and the announced Astrix Security acquisition. Duo handles Agent identity registration and authentication; Astrix focuses on comprehensive Non-Human Identity (NHI) discovery and lifecycle management, covering API keys, service accounts, and OAuth Tokens.
Palo Alto acquired Portkey for $140M ✅ to enter AI Gateway market, integrating guardrails and routing into their security platform. OpenAI's Daybreak defines entry boundaries from the model layer through a three-tier access control model, with partners including Cloudflare, Cisco, CrowdStrike.
Track 2: Assessment Layer Red Team & Vulnerability Discovery
Assessment layer addresses "whether Agents run trustworthiness"—discovering Agent weaknesses and attack risks before deployment. Microsoft and Cisco both pushed here during May Patch Tuesday.
Microsoft's MDASH (Multi-model Defense and Assessment for Secure Handling) is the most impactful assessment product this quarter. Orchestrating 100+ specialized Agents through a five-stage end-to-end vulnerability discovery pipeline, it achieved leading results on CyberGym benchmarks and actually discovered and fixed 16 CVEs ✅. MDASH is positioned as an "engineering-grade vulnerability discovery system," not a runtime guardrail.
Cisco's AI Defense launched Explorer Edition, democratizing enterprise red team capabilities for developers. Features include multi-turn adversarial testing, prompt injection and jailbreak detection, with CI/CD integration for GitHub Actions, GitLab, and Jenkins. The LLM Security Leaderboard provides transparency in model adversarial assessment.
OpenAI's Codex Security is another assessment force. Building threat models automatically from code repositories, identifying attack paths, validating vulnerabilities in isolated environments, and generating patches for human review. Beta phase resolved 3000+ critical and high-severity vulnerabilities ✅.
Track 3: Guardrails Layer Runtime Security
Guardrails layer is the "security shell" during Agent execution, ensuring Agents with legitimate identities cannot breach preset boundaries. NVIDIA leads here.
NVIDIA's open-source OpenShell (Apache 2.0) is one of the most technically impactful releases this quarter. It creates independent sandboxes for each Agent, enforcing kernel-level isolation through Linux Security Modules (Landlock), defining policies across four dimensions: filesystem, network, process, and inference. Policies are declarative YAML, with static policies (filesystem, process) locked at creation and dynamic policies (network, inference) hot-reloadable. Credential management through Provider mechanism injects sensitive info only at runtime.17 platforms integrated OpenShell ✅, including SAP, Cisco, CrowdStrike.
Cisco's DefenseClaw is an open-source guardrail framework integrating OpenShell as the sandbox engine, eliminating manual configuration steps. MCP Gateway provides a unified entry point for Agent-external tool interactions.
Microsoft's Agent 365 has no standalone guardrail product, implementing runtime control through built-in security policies and MCP protocol support, applicable to its own Agent ecosystem.
Track 4: Detection Layer Behavior Monitoring
Detection layer answers "what are Agents actually doing"—behavioral insights and anomaly detection beyond log levels.
Palo Alto's Cortex Cloud 2.0 is the most aggressive product here. Introducing AgentiX—an AI Agent workgroup trained on 1.2 billion real security responses—achieving autonomous cloud risk investigation and remediation. Cloud risk remediation compressed from days to minutes ✅, redefining SOC response benchmarks.
Cisco builds behavior monitoring through Secure Access SSE and AI Defense Runtime. Key innovations include intent-aware monitoring and adaptive risk protection, distinguishing normal Agent tool usage from anomalous cross-domain behaviors, with process-tree-level operation chain tracking.
Microsoft's Copilot Studio and Agent 365 Control Plane provide cross-Agent governance visibility, supporting cost monitoring, permission auditing, and anomaly alerts.
Track 5: Model Layer Security
This is OpenAI's unique track—building security foundations from the model's own capabilities and constraints.
OpenAI's Daybreak is not just a cybersecurity platform but GPT-5.5's capability encapsulation in security dimensions. In the three-tier access model, GPT-5.5-Cyber as the highest-restricted tier opens only to authorized workflows, with stronger account-level monitoring and human review requirements. OpenAI explicitly states all Daybreak capabilities are built on "trust, verification, guardrails, and accountability" ⚠️High Confidence.
OpenAI's Model Spec framework is an attempt at public documentation of model behavior guidelines, open-sourced on GitHub and accepting community review.
Judgments & Recommendations
Agent mass production's security gap will accelerate expansion in H2 2026. Gartner's predicted 40% project cancellation rate won't be uniform—enterprises lacking any layer of the five-layer security architecture face the highest failure risk.
Three priority recommendations for enterprise security decision-makers:
First, complete identity remediation. Deploy Agent identity management solutions, register each Agent as an enterprise Identity Object, bind Sponsors, establish lifecycle management. Microsoft Entra Agent ID and Cisco Duo IAM are the most complete enterprise options.
Second, supplement runtime guardrails. Must establish sandbox isolation before Agent deployment. NVIDIA OpenShell provides the most complete open-source guardrail layer implementation, already widely integrated by major platforms. Choose solutions compatible with your infrastructure.
Third, establish assessment loops. Incorporate red team testing into CI/CD pipelines, continuously assessing Agent security before deployment. MDASH and AI Defense Explorer Edition represent "engineering-grade continuous assessment" direction.
Security infrastructure determines who lands—this is not alarmist but the clearest conclusion behind the 78% pilot failure rate.

💬 Comments (0)